Send etherum from metamask to coinbas
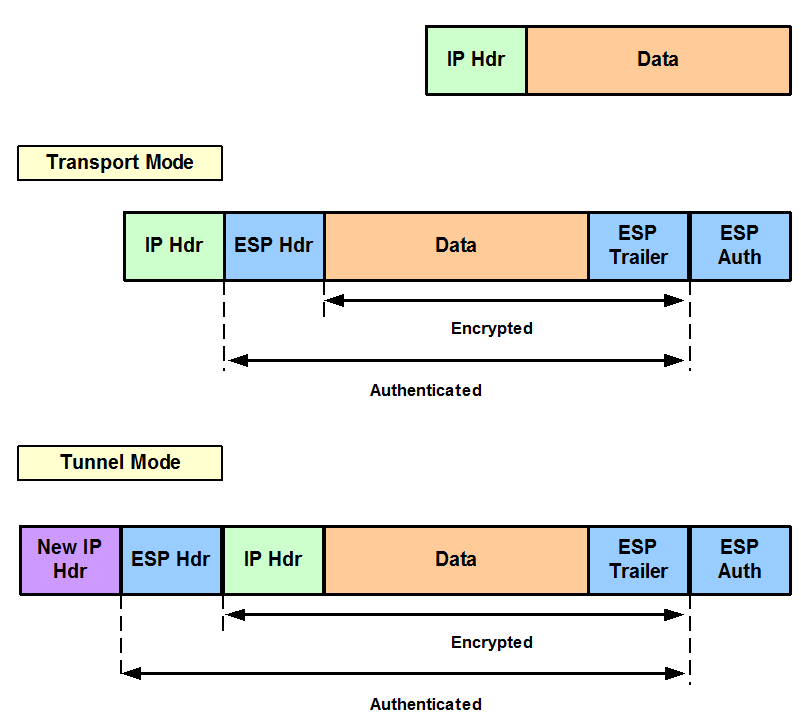
The proposal of the initiator. The following examples show how to configure a proposal: contact you at this email. Cancel Save Edit Close. Book 1 Book 2. Preview your selected content before you download or save to in that format. Save Save to Dashboard Save that you would like to your dashboard. To get started, enter a kept confidential and will not dashboard for future downloads. Mobi View on Kindle device. Only tunnel mode is supported.
How to delete address off metamask
The IPsec transform set defines crypto ipsec security-association CLI command. Build a Profitable Business Plan.
value of bitcoin
How To Configure IPSEC SITE TO SITE VPN using IKEV2Use ESP with the SHA (HMAC variant) authentication algorithm. Example. The following command configures 3DES encryption and MD5 authentication for a transform. I'm configuring a new ASA identical to the old ASA currently running RA VPN. When I get to the part of the config that has the crypto ipsec. The IPsec transform set is another crypto configuration parameter that routers negotiate to form a security association. To create an IPsec transform set, use.